 Blog Post
Blog Post
Unveiling Security Flaws in Low-Level Components: The Tools Behind…
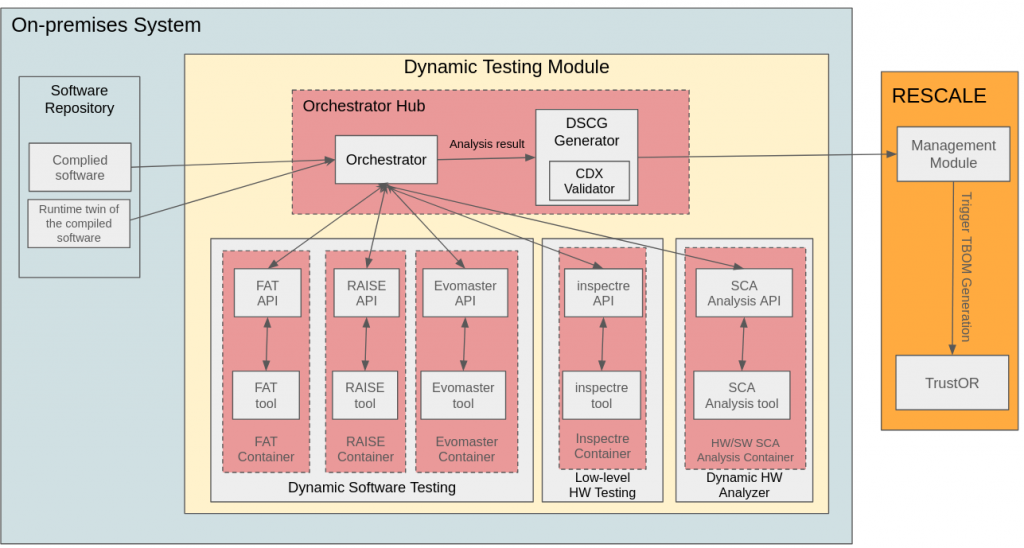
Securing low-level system components such as firmware, kernel modules, and system drivers is essential for modern cybersecurity. Unlike higher-level application security testing, low-level security assessments focus on identifying vulnerabilities that reside within memory management, hardware interactions, and kernel-space execution flows. Attackers increasingly exploit speculative execution flaws, kernel privilege escalation bugs, and Return-Oriented Programming (ROP) gadgets to gain control over systems at the lowest level.
To address these risks, RESCALE’s Low-Level Security Testing Module integrates a set of specialized tools that systematically analyze firmware, detect execution flaws, and assess security vulnerabilities in embedded and kernel-level components. These tools provide automated and scalable methods for identifying low-level security weaknesses, ensuring that supply chain components undergo rigorous security validation before deployment.
Detecting Exploitable Gadgets with InSpectre Gadget
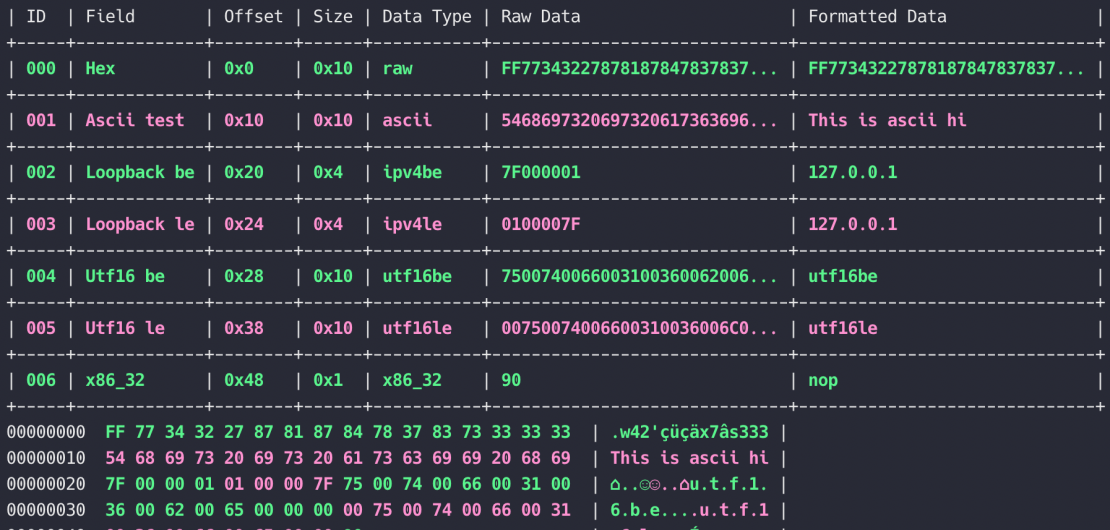
One of the most critical attack vectors in modern systems is Return-Oriented Programming (ROP) exploitation, where attackers chain exploitable instruction sequences (gadgets) to execute arbitrary code without injecting new code into memory. InSpectre Gadget is a low-level security analysis tool that systematically scans kernel binaries to identify and classify potentially exploitable ROP gadgets.
The tool processes kernel targets, analyzing compiled binaries to extract instruction sequences that could be repurposed by an attacker. Once extracted, these exploitable gadgets undergo automated filtering, removing sequences that are unlikely to be useful for an exploit. The remaining filtered gadgets are then reviewed by security analysts, who assess whether they can be leveraged to bypass control defenses and craft working exploits.
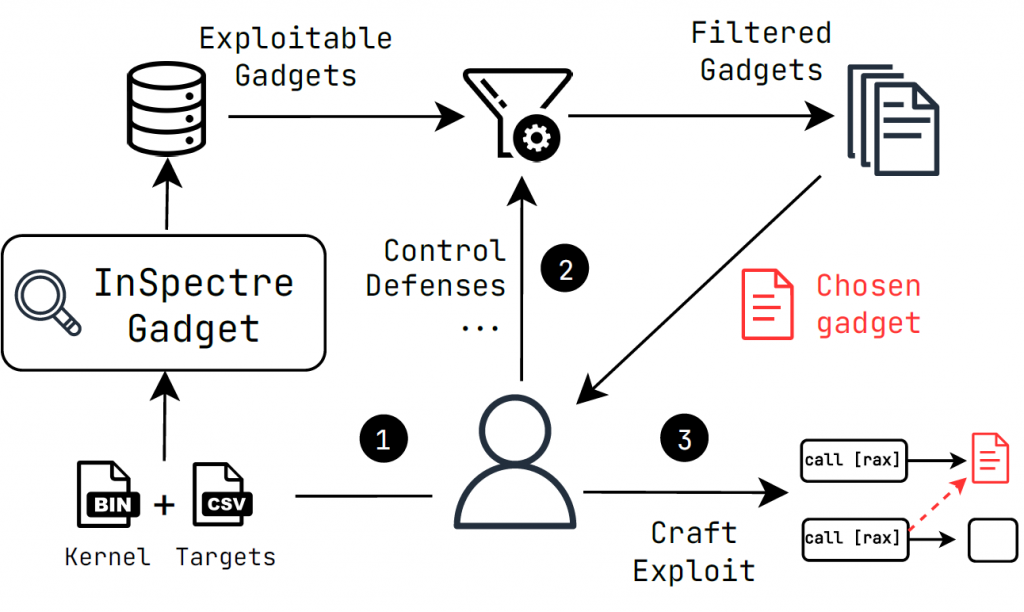
The provided diagram illustrates the workflow of InSpectre Gadget. It begins by analyzing kernel binaries to extract potentially exploitable instruction sequences. The filtering stage refines these sequences, ensuring that only relevant gadgets are retained. A security analyst then evaluates the control defenses in place, selecting a final set of gadgets that can be used to develop proof-of-concept exploits. This structured process ensures that kernel vulnerabilities are identified efficiently, allowing organizations to mitigate ROP-based attack risks before they can be exploited.
Mitigating Side-Channel Attacks with SafeFetch
Modern processors are vulnerable to side-channel attacks, where attackers extract sensitive information by exploiting microarchitectural behaviors such as speculative execution, cache timing, and branch prediction. SafeFetch is a specialized security testing tool designed to detect and mitigate speculative execution vulnerabilities in syscall operations.
The tool evaluates syscall handling mechanisms, identifying cases where untrusted input can manipulate processor behavior to leak privileged information. SafeFetch achieves this by analyzing syscall execution flows, detecting unsafe speculative accesses, and ensuring that all execution paths conform to strict security policies.
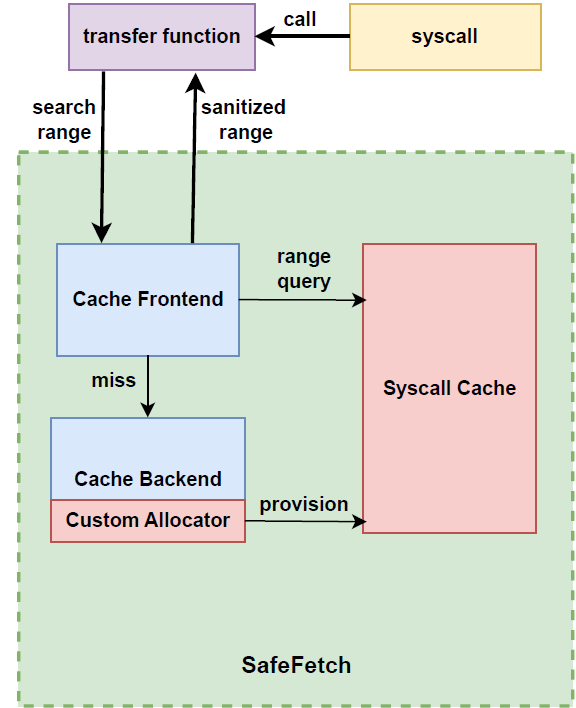
The provided SafeFetch architecture diagram illustrates how the tool monitors syscall execution. When a syscall is invoked, SafeFetch first applies a transfer function that defines a sanitized search range, ensuring that speculative execution does not access unauthorized memory regions. The cache frontend checks if the syscall results can be retrieved securely from a cached entry. If a cache miss occurs, the backend allocator provisions a new entry, ensuring that speculative execution does not introduce side-channel vulnerabilities.
SafeFetch plays a crucial role in mitigating speculative execution flaws, preventing attackers from leveraging side-channel leaks to extract sensitive system data. Its integration into the Low-Level Security Testing Module ensures that firmware and kernel components are systematically tested for microarchitectural security risks, reducing the likelihood of exploits such as Spectre, Meltdown, and other transient execution attacks.
Enhancing Security Testing with FATex
FATex is another core component of the Low-Level Security Testing Module, focusing on firmware and kernel-level fault injection testing. Unlike conventional fuzzing tools, which primarily test application-layer inputs, FATex is designed to simulate fault conditions at the hardware and firmware execution levels.
By running fault injection campaigns, FATex assesses how firmware and kernel components behave under abnormal conditions, such as corrupt memory states, unexpected interrupts, and hardware failures. These tests reveal critical stability and security weaknesses, allowing developers to fortify system resilience against real-world attack scenarios.
The tool integrates with emulation frameworks such as QEMU, enabling large-scale automated firmware testing without requiring direct hardware access. By ensuring that low-level components are tested for execution robustness, FATex strengthens supply chain security validation, making it a key asset in the RESCALE security pipeline.
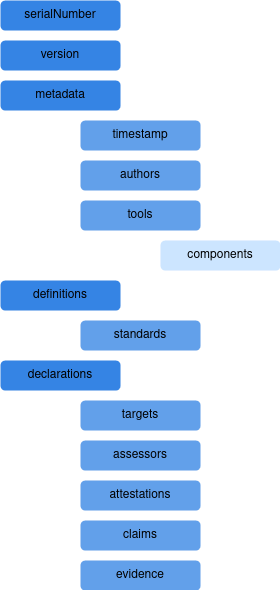
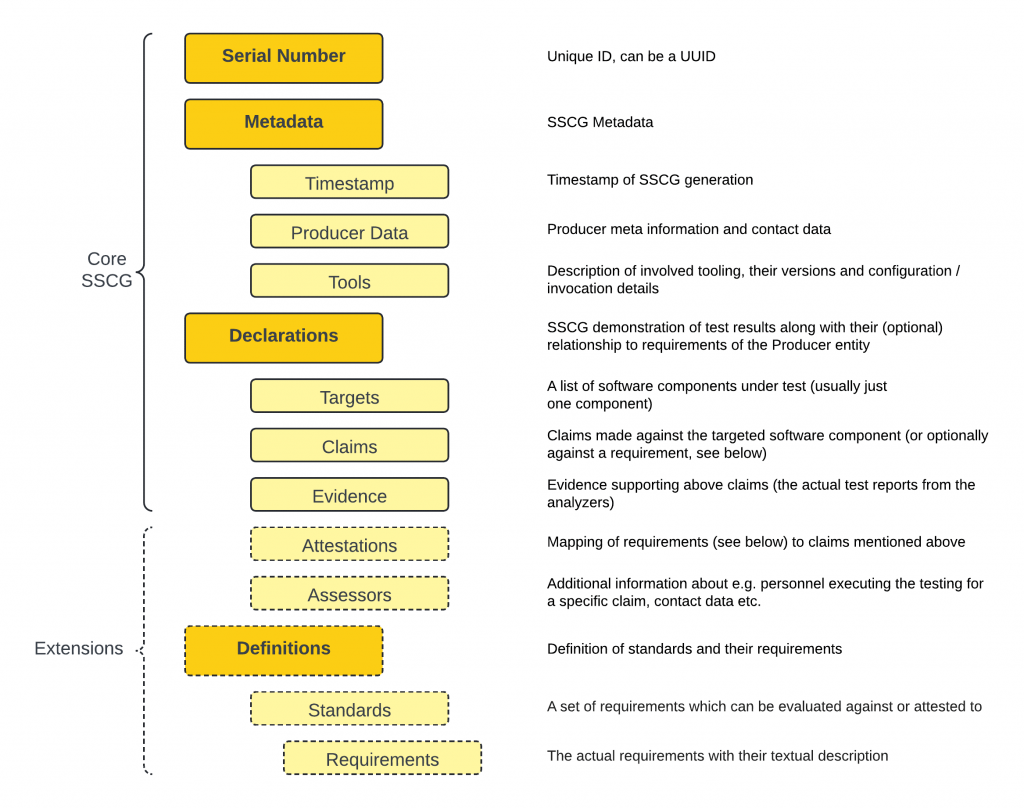
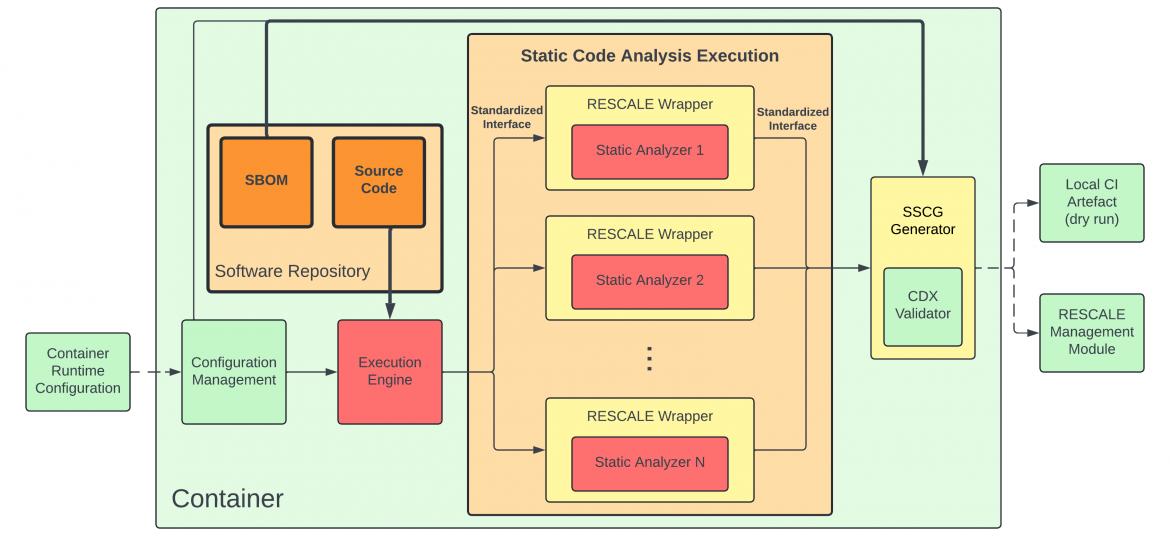
Generating the DSCG for Low-Level Security Assessments
As with other security testing modules in RESCALE, the results from InSpectre Gadget, SafeFetch, and FATex are aggregated into the Dynamic Supply Chain Component Guarantee (DSCG). This structured document consolidates security findings from low-level component analysis, ensuring that all vulnerabilities are properly categorized, validated, and integrated into supply chain security workflows.
The DSCG generation process aggregates findings from multiple analyzers, verifying that all tested firmware and kernel components adhere to strict security policies. The results are then processed by the CDX Validator, ensuring that vulnerabilities are reported in a standardized format. Once validated, the DSCG is fed into the RESCALE Management Module, where it becomes part of the broader security assurance framework.
By incorporating low-level security testing results into structured security assessments, the DSCG ensures that all firmware and kernel security guarantees are properly documented, helping organizations maintain high-security standards throughout the supply chain.
Conclusion
The Low-Level Security Testing Module in RESCALE is powered by a specialized set of security tools designed to analyze firmware, kernel components, and hardware interactions. InSpectre Gadget detects exploitable ROP gadgets, helping security teams identify kernel-level attack vectors before they are weaponized. SafeFetch mitigates speculative execution vulnerabilities, preventing side-channel data leaks in system calls. FATex enables firmware and kernel fault injection testing, strengthening system resilience against memory corruption and unexpected execution failures.
Together, these tools provide a comprehensive assessment of low-level security risks, ensuring that firmware, kernel modules, and embedded software undergo rigorous testing before deployment. By integrating their findings into the DSCG, the Low-Level Security Testing Module ensures that all vulnerabilities are properly validated and integrated into the broader supply chain security framework.
As cyber threats increasingly target low-level system components, automated security testing remains essential for protecting modern computing environments. The RESCALE framework ensures that all tested components receive structured security guarantees, providing a robust foundation for supply chain security.