News
News
 News
News
Home » Archives for leka » Page 2
 News
News
The RESCALE Plenary Meeting was held in Braunschweig, Germany, on June 22–23, 2025. Hosted by AEGIS IT RESEARCH, the meeting gathered project partners to review progress, align on key objectives, and discuss next steps for delivering secure-by-design solutions aimed at enhancing supply chain security.
Over the course of two days, participants engaged in productive exchanges of ideas, workshops, and technical discussions, setting the stage for the next phase of the project.
We extend our gratitude to AEGIS IT RESEARCH for their excellent organization and warm hospitality, which contributed significantly to the meeting’s success.
Stay tuned for further updates as RESCALE advances its mission to strengthen cybersecurity in supply chains.

 Blog Post
Blog Post
Supply chains form the backbone of modern industries, and their resilience is a cornerstone of operational security. While much of the discourse around supply chain vulnerabilities focuses on conventional cybersecurity risks, such as software vulnerabilities or malicious actors, side-channel vulnerabilities present an equally critical, yet often underestimated, threat. These vulnerabilities exploit indirect information leaks, such as timing, power consumption, or electromagnetic emissions, to infer sensitive data. The impact of such attacks on software and hardware supply chains can be devastating, leading to compromised components that cascade failures across dependent systems.
In this article, we delve into the nature of side-channel vulnerabilities in supply chains, examine their implications, and discuss emerging methodologies to mitigate these risks.
Side-channel attacks exploit unintended information channels that arise from the physical implementation of software or hardware components. Unlike direct attacks that target software flaws or network vulnerabilities, side-channel attacks leverage physical characteristics, such as:
While side-channel vulnerabilities have traditionally been studied in the context of cryptographic systems, their impact on supply chains is equally profound. Components affected by these vulnerabilities can serve as entry points for attackers, compromising the integrity of the entire supply chain.
Side-channel vulnerabilities represent a critical yet underexplored dimension of supply chain security. The RESCALE project, emphasising secure-by-design supply chains, is uniquely positioned to address these risks. By integrating advanced analysis tools, fostering transparency through TBOM frameworks, and advocating for robust security standards, we can mitigate the cascading threats posed by side-channel attacks. The call to action is clear: organisations must prioritise side-channel resilience within their
supply chain strategies to safeguard the integrity and trust of their systems.
 Blog Post
Blog Post
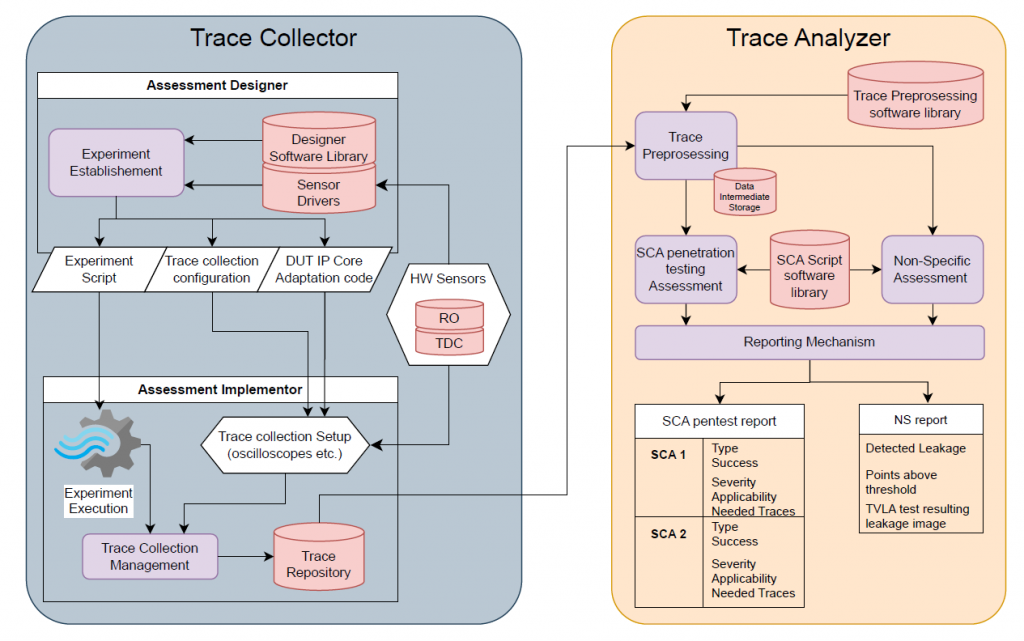
Detecting and mitigating hardware vulnerabilities requires specialized tools capable of extracting, processing, and analyzing physical security risks within cryptographic and FPGA-based systems. The Dynamic Hardware Analyzer (DHA) in RESCALE is built around a suite of tools designed to identify side-channel leakage, detect exploitable vulnerabilities, and assess security risks in hardware implementations. These tools focus on trace collection, preprocessing, and attack simulations, ensuring that supply chain components undergo rigorous security validation before deployment.
To detect hardware vulnerabilities, the first step is capturing physical traces from the target system. The Trace Collection Layer of the Dynamic Hardware Analyzer includes several specialized tools that record power consumption, electromagnetic emissions, and timing variations during cryptographic operations. These traces serve as the foundation for further analysis.
One of the primary tools in this layer is FlexLECO, an FPGA-based leakage assessment framework that performs large-scale trace collection and real-time monitoring. Unlike conventional power measurement tools, FlexLECO integrates directly with FPGA implementations, enabling high-speed acquisition of side-channel signals while minimizing measurement interference. Additionally, the system leverages ChipWhisperer, a well-known open-source platform designed for side-channel attack research. ChipWhisperer captures power consumption fluctuations during cryptographic operations, allowing security analysts to detect unintended leakage paths.
Another key tool in the trace collection phase is the use of on-chip FPGA sensors, which monitor transient power variations and signal fluctuations at an extremely fine-grained level. These sensors allow for low-noise trace acquisition, making it possible to detect even minimal leakage that could expose cryptographic keys or other sensitive data.
Once traces are collected, they must undergo preprocessing to filter out noise and highlight relevant leakage information. The Trace Preprocessing Software Library plays a crucial role in this phase by applying signal filtering, normalization, and correlation analysis techniques. This ensures that collected traces are clean, structured, and ready for in-depth security assessment.
This software suite applies statistical tests such as Test Vector Leakage Assessment (TVLA) to determine whether the captured traces exhibit unintended data-dependent variations. TVLA is the primary statistical method used in RESCALE for evaluating cryptographic leakage. It helps identify leakage points where cryptographic implementations may be revealing sensitive information. These points appear as deviations in signal quantification, which can be statistically analyzed to determine the likelihood of an exploitable vulnerability.
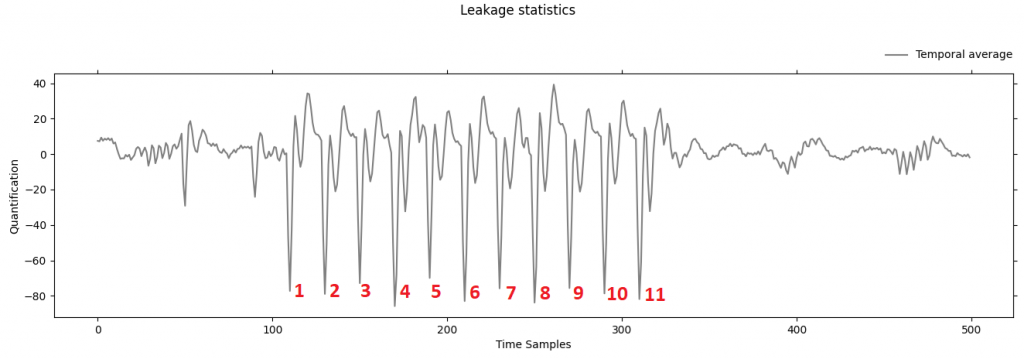
The AES Leakage Plot above illustrates the results of a TVLA leakage test. The graph visualizes quantification over time samples, with several identified peaks that indicate points of significant leakage. These leakage points suggest areas where cryptographic keys or sensitive operations might be unintentionally exposed, requiring further investigation to assess their exploitability. The presence of strong deviations in power consumption signals at specific time samples confirms that certain cryptographic operations may be leaking data in a manner detectable through side-channel analysis.
After preprocessing, the SCA Script Software Library is used to conduct security evaluations and attack simulations. This toolset applies correlation power analysis (CPA), machine-learning-based template attacks, and non-specific (NS) assessments to determine whether an attacker could extract sensitive information from the collected traces.
The CPA method is particularly effective in identifying linear relationships between power consumption and cryptographic key bits, making it a widely used attack technique against AES, RSA, and other encryption standards. In contrast, machine-learning-based template attacks leverage pre-trained statistical models to recognize leakage patterns, even in the presence of noise or countermeasures.
The NS assessment approach is used to detect leakage without assuming a specific attack model. This technique helps analysts identify general leakage trends before applying targeted cryptographic attack models like CPA. NS assessment is particularly useful in discovering unexpected security weaknesses that might not align with traditional attack strategies, ensuring a broader evaluation of side-channel resilience.
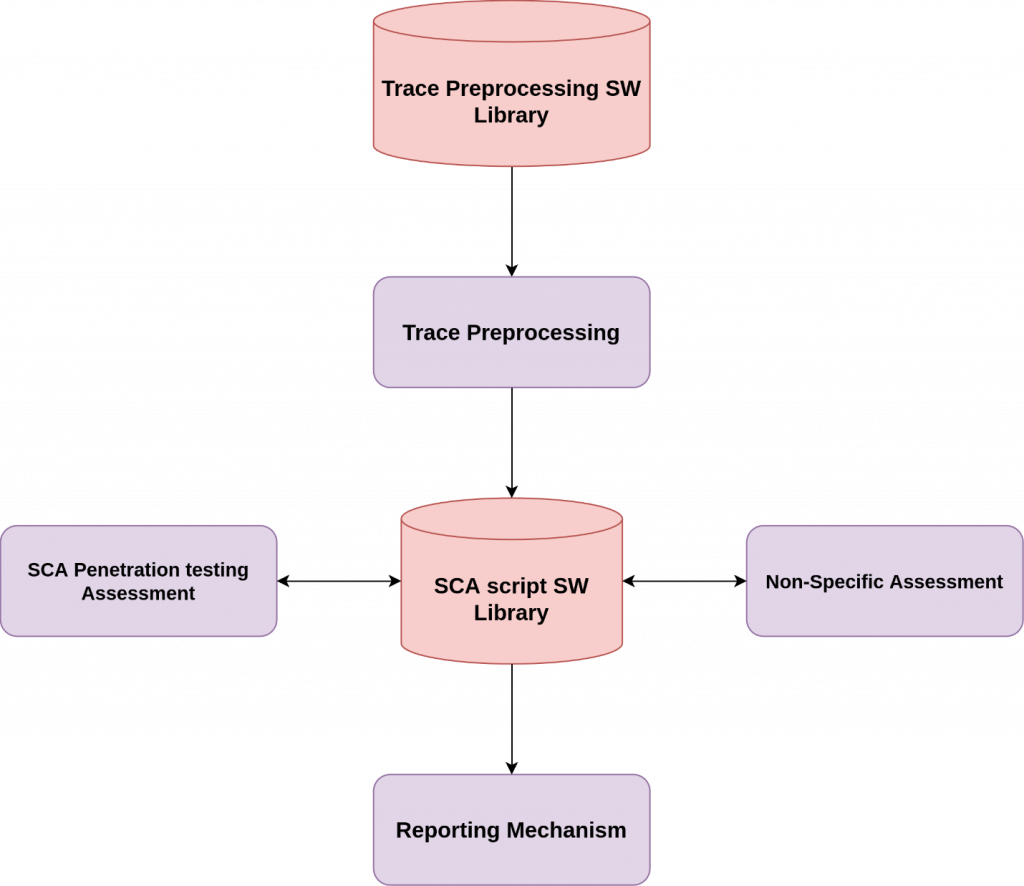
The SCA Trace Analyzer Flow diagram illustrates the relationship between preprocessing, penetration testing, and reporting within the Dynamic Hardware Analyzer. At the core of this system, the Trace Preprocessing Software Library processes collected traces, applying signal filtering and statistical assessments. The SCA Script Software Library then runs advanced side-channel attack models, including SCA penetration testing assessments, which attempt to exploit detected vulnerabilities. The results are structured into NS reports and SCA pentest reports, feeding into broader supply chain security validation efforts.
One of the unique challenges addressed by the Dynamic Hardware Analyzer is the security of multi-tenant FPGA environments. When multiple users share the same FPGA fabric, one user may unintentionally or maliciously extract information from another user’s operations, leading to data leakage risks.
To analyze this threat, the DHA integrates tools that simulate cross-tenant leakage scenarios, measuring how shared hardware resources expose unintended data flows. These tests assess whether attackers can infer cryptographic computations performed by another tenant, helping to enforce stricter FPGA isolation policies.
The final step in the hardware security analysis process is structuring the collected findings into a standardized security report. The results from FlexLECO, ChipWhisperer, and the SCA Script Software Library are aggregated into the Dynamic Supply Chain Component Guarantee (DSCG). This structured document provides a comprehensive assessment of detected vulnerabilities, categorizing them based on severity, exploitability, and recommended mitigations.
The CDX Validator processes these reports to ensure they adhere to standard security assessment frameworks. Once validated, the DSCG is integrated into the RESCALE Management Module, contributing to supply chain security assurance and risk mitigation strategies.
The Dynamic Hardware Analyzer in RESCALE is powered by a sophisticated suite of tools designed to capture, process, and analyze side-channel leakage data. FlexLECO and ChipWhisperer provide high-resolution trace collection, while on-chip FPGA sensors enable real-time monitoring of leakage effects. The Trace Preprocessing Software Library ensures high-quality signal processing, while the SCA Script Software Library applies advanced CPA, machine-learning, and non-specific analysis techniques to detect vulnerabilities.
By aggregating results into the DSCG, the module provides structured security assessments that contribute to supply chain risk management. As hardware security threats continue to evolve, automated security testing tools remain essential for ensuring that cryptographic and FPGA-based systems remain resistant to side-channel attacks and unintended leakage risks.
 Blog Post
Blog Post
As modern computing systems become more interconnected, the need for hardware-level security has never been more critical. While traditional security measures focus on software vulnerabilities, attackers increasingly exploit low-level hardware flaws to bypass security protections, extract sensitive information, or launch side-channel attacks. Hardware vulnerabilities are particularly dangerous because they often persist across software updates and may not be easily patched once a system is deployed.
Within the RESCALE project, the Dynamic Hardware Analyzer is specifically designed to address these risks by detecting and analyzing hardware vulnerabilities and leakage threats. By employing advanced security testing techniques, the module helps uncover side-channel attack (SCA) risks, power analysis vulnerabilities, and data leakage threats in cryptographic and FPGA-based systems
Hardware vulnerabilities can arise due to various factors, including design flaws, unintended electromagnetic emissions, power fluctuations, or signal timing variations. Unlike software-based vulnerabilities, these issues cannot be fixed with a simple patch; instead, they require thorough detection and mitigation strategies before deployment.
One of the most concerning classes of hardware threats is side-channel attacks. These attacks do not directly exploit software bugs but rather take advantage of unintended physical leakages such as power consumption, electromagnetic emissions, or execution timing. SCAs are particularly effective against cryptographic hardware implementations, allowing attackers to extract secret encryption keys by analyzing physical behavior rather than breaking the encryption algorithm itself.
The Dynamic Hardware Analyzer in RESCALE is designed to systematically detect such vulnerabilities, ensuring that hardware security risks are identified before attackers can exploit them.
The Dynamic Hardware Analyzer is an advanced security testing module that evaluates hardware components, cryptographic accelerators, and FPGA-based designs for security weaknesses. Its primary role is to collect, process, and analyze side-channel leakage traces, determining whether a system exhibits security flaws that could be exploited through power analysis, timing attacks, or other forms of SCAs.
The process begins with trace collection, where the analyzer captures physical side-channel data from hardware devices during cryptographic operations or other sensitive computations. Once collected, these traces undergo trace preprocessing, where signal processing techniques and statistical methods such as the Trace Preprocessing Software Library and SCA Script Software Library are applied to remove noise and extract useful security insights. Finally, the system conducts attack simulations and risk assessments, leveraging Test Vector Leakage Assessment (TVLA) tests and NS report-based analysis to determine whether an attacker could successfully exploit the detected leakages.
These steps ensure a comprehensive evaluation of hardware security risks, helping organizations strengthen their supply chain security before deploying critical hardware components.
The architecture of the Dynamic Hardware Analyzer is structured to efficiently process side-channel leakage data and detect potential hardware vulnerabilities. It consists of several key components that work together to analyze security risks in cryptographic implementations and FPGA-based systems.
As illustrated in the Dynamic Hardware Analyzer architecture, the module consists of three main layers: the Trace Collection Layer, the Trace Analysis Layer, and the Evaluation and Reporting Layer. The Trace Collection Layer is responsible for capturing side-channel data such as power consumption, electromagnetic emissions, or execution timing variations from a target hardware system. This data is then transferred to the Trace Analysis Layer, where advanced statistical methods, correlation analysis, and machine learning models process the information, identifying whether the hardware leaks sensitive information. Finally, the Evaluation and Reporting Layer integrates these findings into structured security reports, ensuring that vulnerabilities are properly categorized and assessed.
This layered architecture ensures that security assessments are not only comprehensive but also scalable, allowing multiple hardware components to be evaluated within a controlled environment. By structuring the analysis process in a modular way, the Dynamic Hardware Analyzer can be adapted to different hardware platforms, making it a versatile tool in RESCALE.
The Dynamic Hardware Analyzer does not function in isolation. It is fully integrated into the broader RESCALE security pipeline, ensuring that hardware security risks are assessed alongside software vulnerabilities. The findings from the module contribute directly to RESCALE’s Trusted Bill of Materials (TBOM), consolidating security guarantees across the entire supply chain.
By working in conjunction with other security modules, such as the Static Code Analysis Module and the Low-Level Security Testing Module, the Dynamic Hardware Analyzer ensures that both hardware and software components undergo rigorous security validation before deployment. This multi-layered security approach strengthens the overall resilience of computing systems, helping organizations detect, analyze, and mitigate hardware security threats before they become a liability.
Hardware vulnerabilities are becoming an increasingly attractive target for advanced persistent threats (APTs) and state-sponsored attacks. Unlike software exploits, which can often be mitigated through patches and updates, hardware flaws may persist throughout a device’s lifecycle, making early detection crucial.
By integrating hardware security testing into supply chain security practices, organizations can reduce the risk of data breaches, intellectual property theft, and cryptographic key extraction. The Dynamic Hardware Analyzer in RESCALE ensures that hardware vulnerabilities are systematically detected and addressed, reinforcing the security of critical computing infrastructure.
The Dynamic Hardware Analyzer in RESCALE is a key component in modern hardware security testing, providing organizations with the ability to detect, analyze, and mitigate hardware-level vulnerabilities before they can be exploited. By leveraging advanced trace collection, preprocessing, and side-channel attack detection techniques, the module plays a crucial role in strengthening supply chain security.
By integrating with the broader RESCALE security framework, the module ensures that low-level security assessments contribute to the overall supply chain security process. In the next article, we will explore the specific tools and methodologies used within the Dynamic Hardware Analyzer, including trace collection devices, machine learning-based SCA detection techniques, and advanced cryptographic leakage assessments.
 News
News
The 3rd RESCALE plenary meeting was successfully held in Amsterdam, Netherlands, on December 6-7, 2024, hosted by Stichting VU (VUA). Over two days of engaging discussions, interactive workshops and valuable feedback, the consortium made significant strides in finalizing the first release of the RESCALE platform. Partners collaborated on the latest advancements in cybersecurity, supply chain security and tool integration, ensuring RESCALE continues to drive innovation in the field. A huge thank you to all partners for their contributions and to VUA for hosting us! Stay tuned for more updates as we move forward.

 News
News
The 1st RESCALE technical meeting took place at the University of Piraeus, Athens, Greece, on December 10-11, 2024. Hosted by University of Piraeus Research Center (UPRC), the meeting focused on DSCG and SSCG generation and tool integration, bringing together technical experts to enhance supply chain security.
Stay tuned for more updates as RESCALE continues its mission to revolutionize supply chain cybersecurity!